How To Mitigate CVE-2023-22374- A High Severity Format String Vulnerability In F5 BIG-IP Products? - The Sec Master
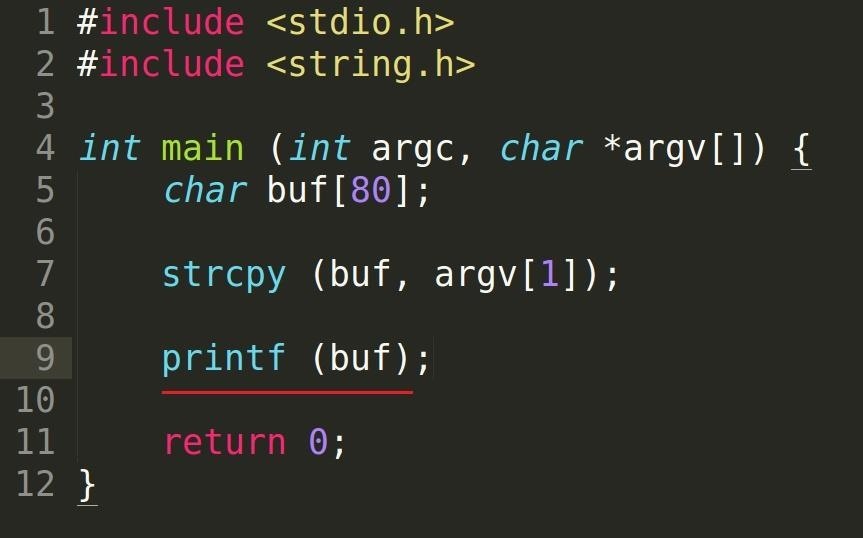
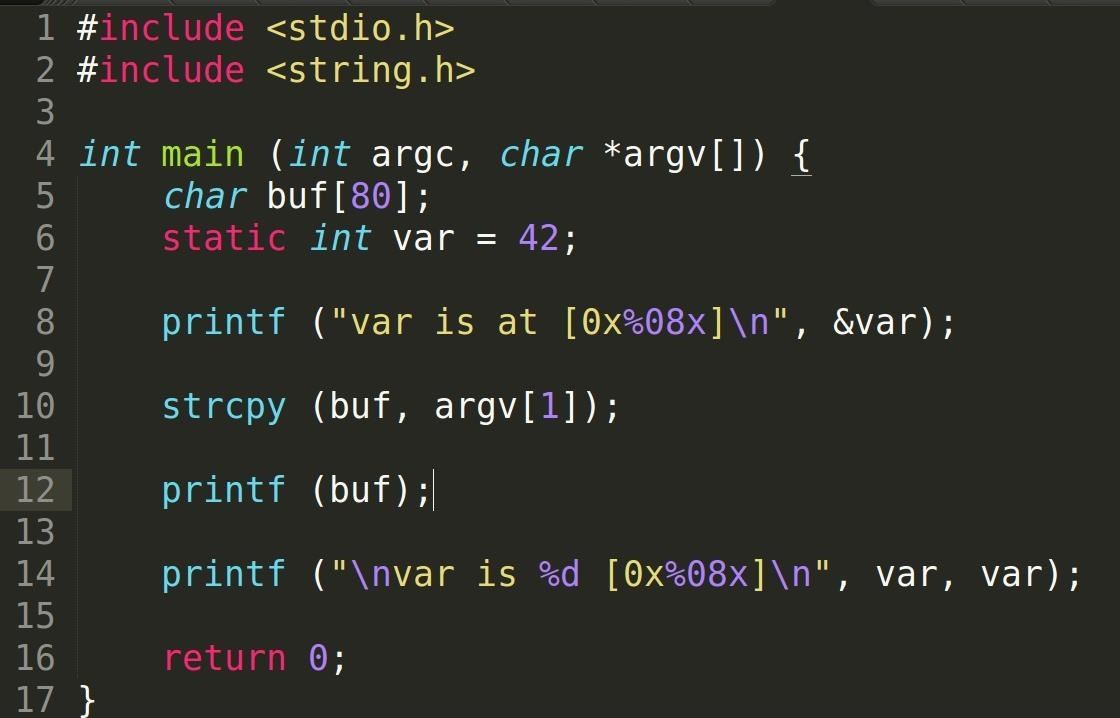
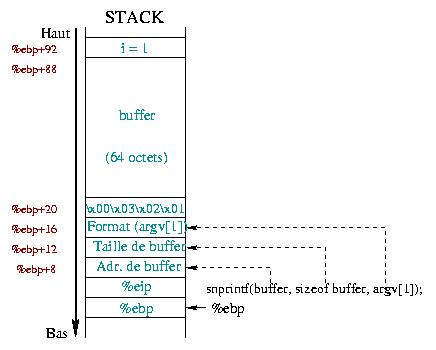
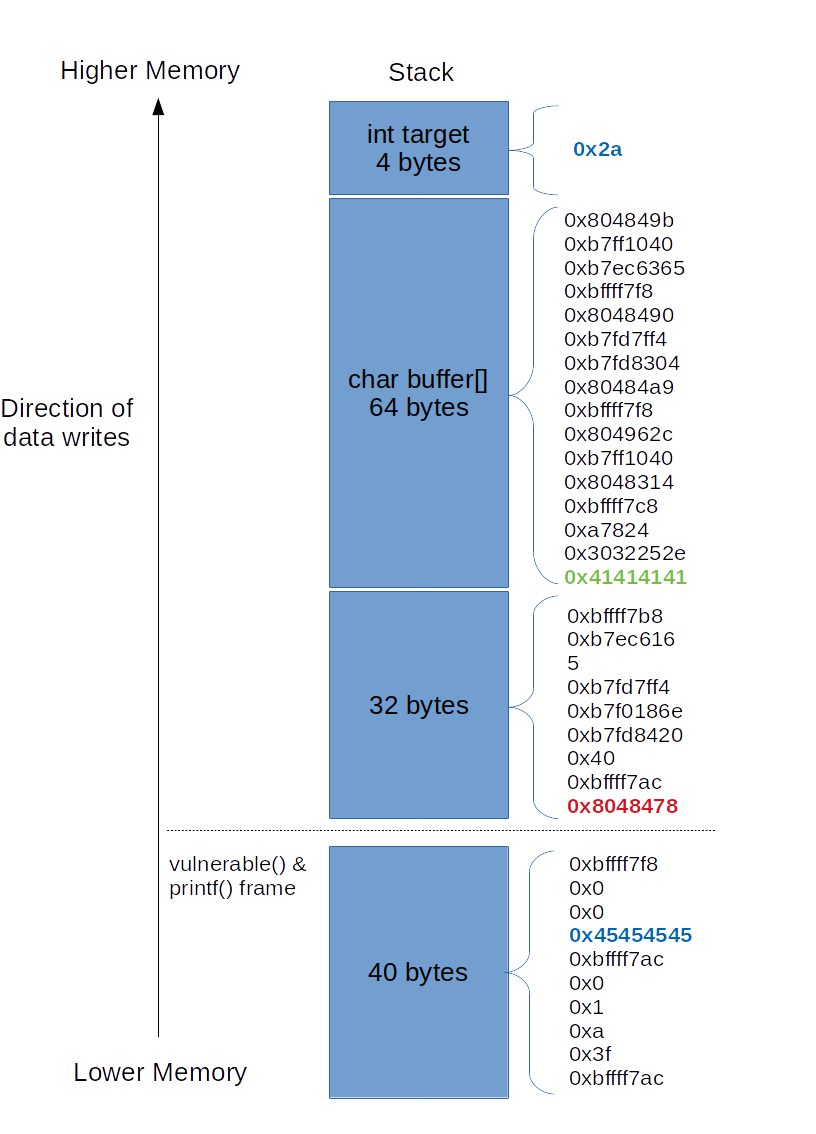
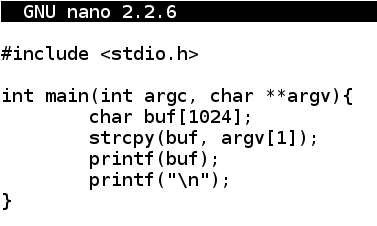
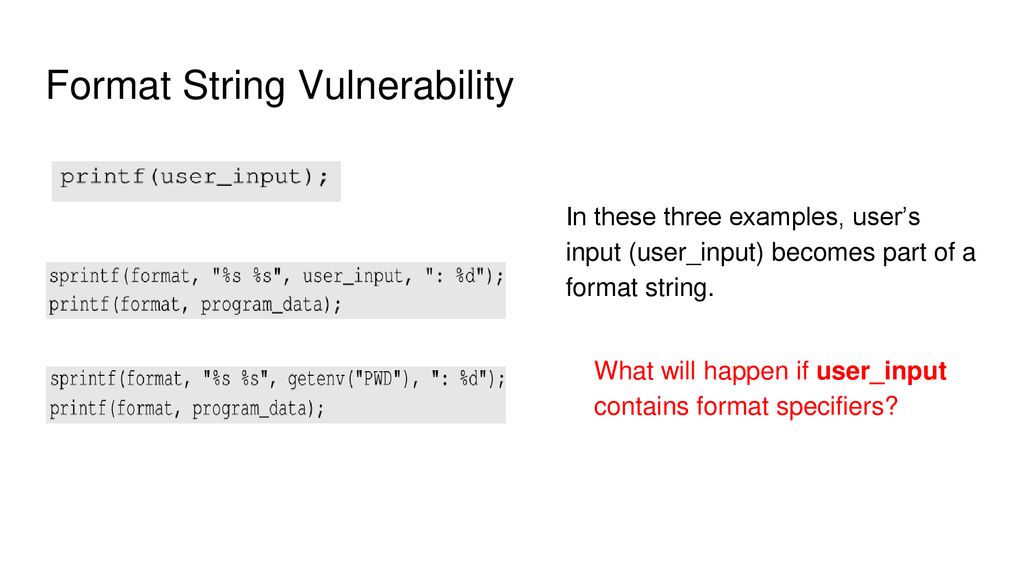
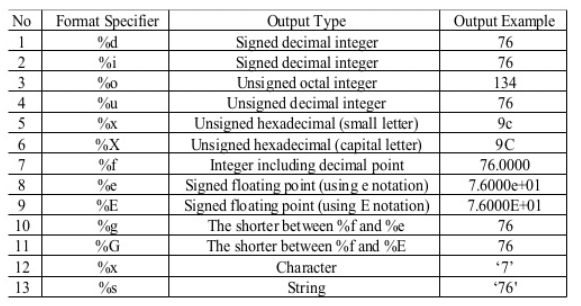
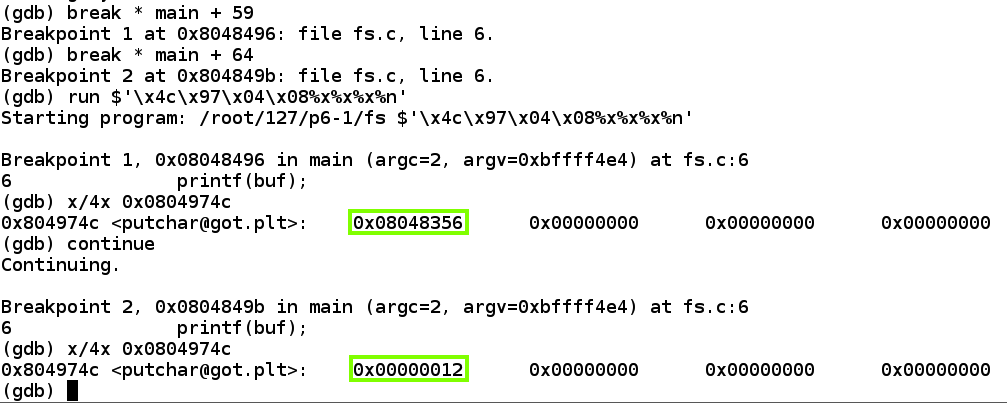
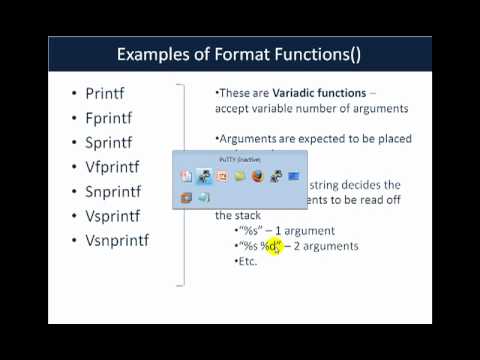
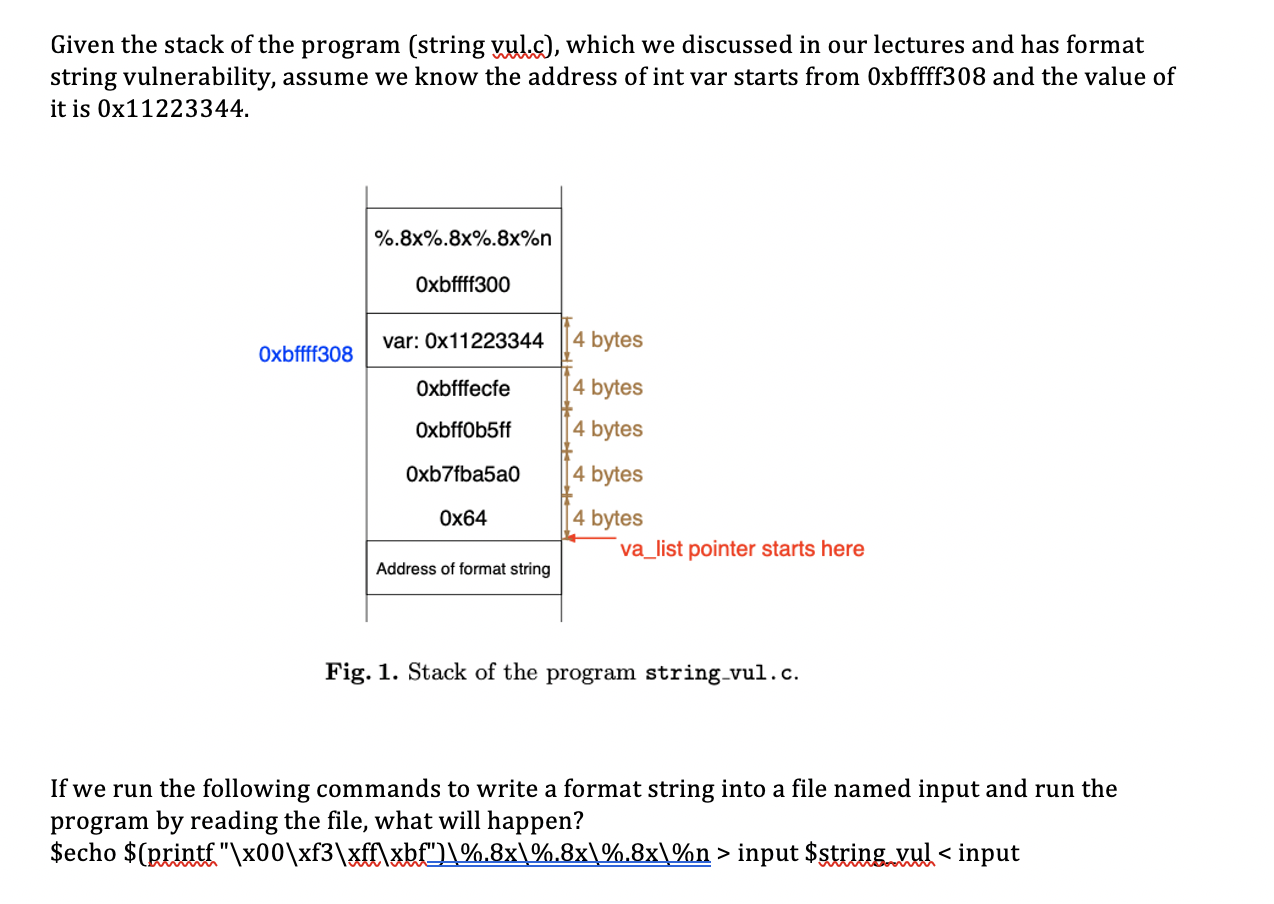
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother « Null Byte :: WonderHowTo
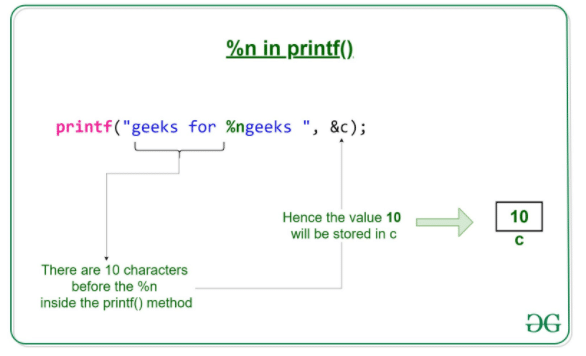
13.7 Format String Bugs :: Chapter 13. Application-Level Risks :: Network security assessment :: Networking :: eTutorials.org
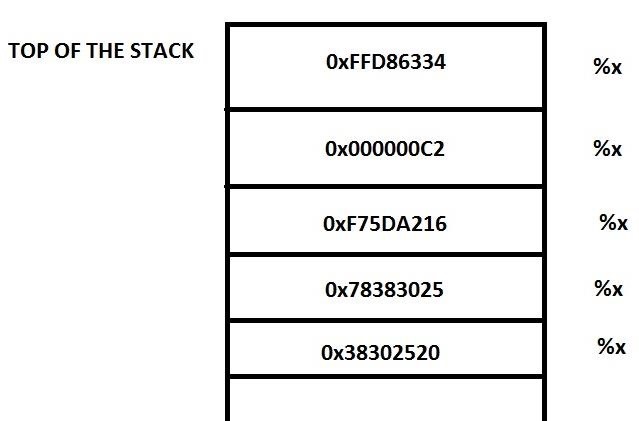
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother « Null Byte :: WonderHowTo